Enrollment Guide
The enrollment guide is organized into four main sections, each providing detailed instructions for the different types of device enrollments available for Android, Apple, and Windows devices:
Each section provides comprehensive explanations and procedures tailored to the specific device types:
| Android Enrollment Guide | iOS Enrollment Guide | macOS Enrollment Guide | Windows Enrollment Guide |
|---|---|---|---|
| Install Entgra Android Device Management Agent | Additional Server Configurations | Enroll macOS Device Manually | Windows Server Configuration |
| Android Enrollment Configurations | Apple (iOS and MacOS) Server Configurations | Entgra Windows Device Management Agent Deployment | |
| Enroll Android Devices | Apple (iOS and MacOS) DEP Configurations | Enroll Windows Device | |
| Enrollment Issue Diagnosis |
Android Enrollment Guide
Note
- Before enrolling, make sure to set up Android Enrollment Configurations in the Configurations section.
- Install the Entgra Android Device Management Agent. Note that this step is only necessary for enrollment modes other than QR enrollment after a factory reset.
Install Entgra Android Device Management Agent
Android devices are enrolled and managed using an application that is installed on the device, known as the Device Management Agent App.
The Entgra Agent app can be installed by downloading it in two ways:
Download from Entgra UEM server
Download from Entgra UEM server
There is an agent app bundled with the UEM server that can be downloaded to your mobile device and installed.
Prerequisites
- The server has to be downloaded and started.
- Must have been logged on to the server's Endpoint Management Portal.
Steps
- Go to the Enroll Device section.
- Select Android under device types.
- Scan the QR code using the Android device. (New Android OS versions include the QR code scanning app in-built. If this is not available, a QR code scanning app can be downloaded from the Play Store)
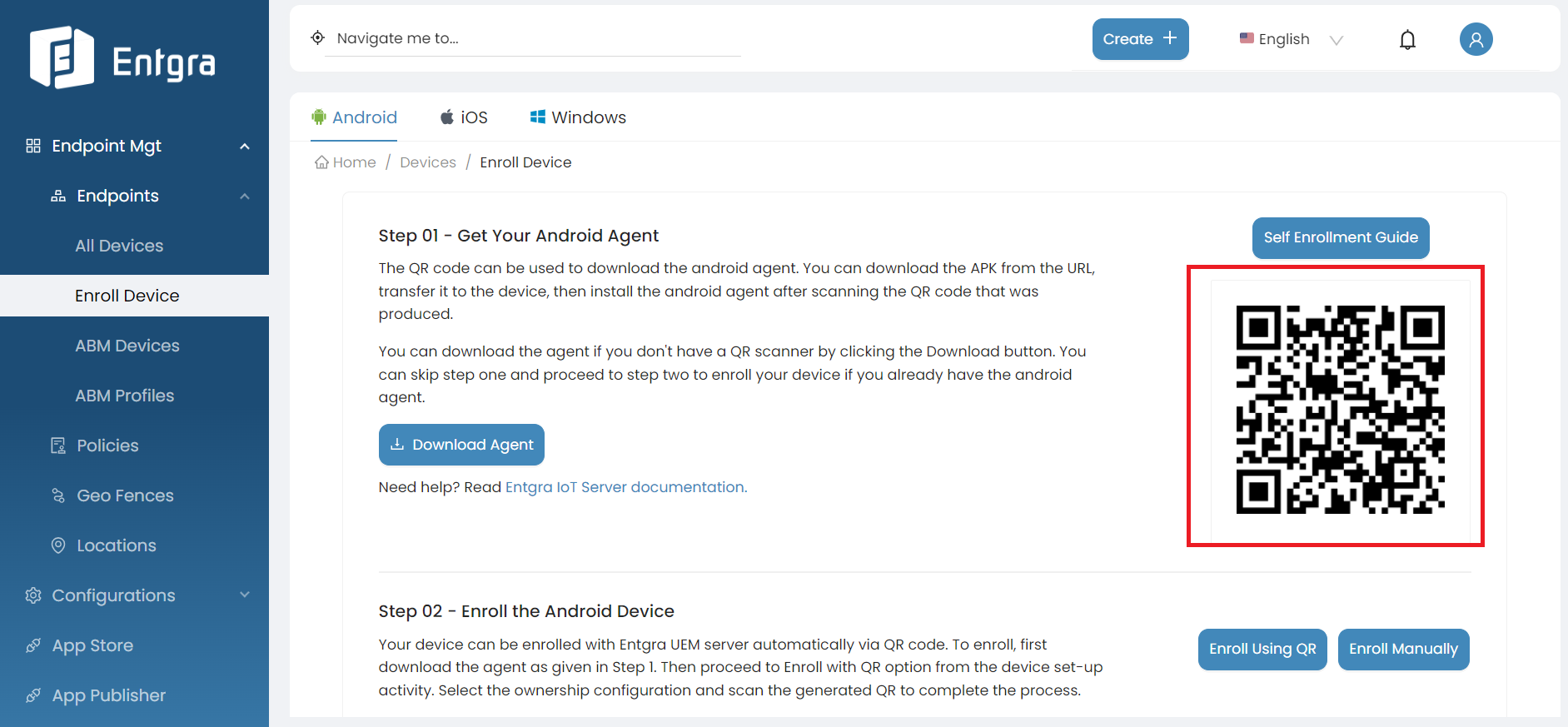
- Follow the QR code scanned link to download the agent to the device.
Alternatively, this page can be accessed via the mobile device browser itself
- Follow steps 1-2 on the phone’s browser.
- Click on Download Agent to download the APK to the device.
- Once the app is downloaded, click Open.
- Depending on the OS version of the device, unknown sources has to be enabled to install the agent. In Android 8 and upwards, once you click Open, the following screen will be displayed. Select Allow from this source and go back.
- Click Install to install the agent.
Download from the Playstore
Download from the Playstore
Visit the link https://play.google.com/store/apps/details?id=io.entgra.iot.agent using your mobile device or go to the Google Play Store app on the mobile device and search for Entgra Device Management Agent and install the app.
Android Enrollment Configurations
To successfully initiate the enrollment process, ensure that the following configurations are set up:
Android Platform Configurations
Please follow the Configurations section for setting up Android Platform Configurations.
QR Configurations
- Go to the Enroll Device section.
- Select Android under device types.
-
Select Enroll Using QR under the step 2.

-
Click the Settings icon.

-
You can set up following configurations before generating the QR code.

Define the Provision Mode
Select the connectivity mode to be used during the device enrollment process. The available options are:
-
Wi-Fi: Use a Wi-Fi network to connect the device for enrollment.
Key Description Wifi SSID Wifi SSID cannot be a hidden network(not broadcasting) Wifi Security Type Wi-Fi security type of network should be WPA/WPA2-psk Wifi Password Password of the Wi-Fi network -
Mobile Data: Use a mobile data connection for device enrollment.
Note
Please note that the mobile data connection option is available only for Android devices running version 13 and above. Do not use this option for devices running Android versions below 13.
Token Expiry Configurations
Customize the validity period of the QR codes by setting the token expiration time. The duration should be specified in hours and minutes, using the format [0-*]:[0-59]. For example, 3 hours and 5 minutes should be entered as 3:05.
Enroll Android Devices
This section describes the types of enrollment available for Android Devices and how to enroll an Android device. The available enrollment types are:
- Bring Your Own Device (BYOD)
- Corporately-Owned Personally-Enabled (COPE)
- Dedicated Device Enrollment (COSU/KIOSK)
- Google Work Profile
- Fully Managed
- Azure AD Integrated Enrollment - Just In Time Provisioning
BYOD Enrollment
BYOD Enrollment AKA Legacy enrollment allows you to manage settings and apps on the device. This type of enrollment offers wider control over the device allowing features such as the ones indicated below:
-
Factory Reset Protection (FRP) - for managing devices and for recovering in the event of employee leaving.
-
Reset device passwords - secure this feature on encrypted devices. Block removal of the device administrator.
-
Admin controlled passcodes - that enable locking the user out of a device.
Available enrollment modes for BYOD enrollment:
BYOD Manual Enrollment
Prerequisites
- The server has to be downloaded and started.
- Must have been logged on to the server's Endpoint Management Portal.
- Install Entgra Android Agent on your android device.
- Optionally, Basic Concepts of Android Device Management will be beneficial as well.
Steps
- Open the Entgra Agent application on your android device.
- Click Continue after reading the Disclaimer that appears.
- Click on Manual Enrollment.
- On the next screen that appears next, click BYOD Enrollment.
- Click Skip And Go To Enrollment on the screen that appears next.
- Type in the server address which is the IP of the server and port as
8280. If you are using Entgra Cloud, type cloud server address here. Click Start Registration. - Type in the Username:
admin, Password:adminthen click Sign In. If you are an Entgra Cloud user, please do add your organization(tenant) name as well. - If you agree to the policy agreement that is shown next, click Agree to proceed.
- Click Activate on the device screen to enable Entgra Device Management Agent as a device admin app.
- Click Allow if you agree to the request for permissions for access to the device as indicated.
- Click Allow if you agree to use data usage monitoring to allow the server to check the data usage of the device.
- Allow the agent to change Do not Disturb status which is used to ring the device.
- Enter and confirm a PIN code, which is required by the administrator to perform any critical tasks with user consent. Then click Set PIN Code to complete the enrollment.
- Click Allow to enable Entgra IoT Remote Touch.
Video Tutorial for BYOD Manual Enrollment
Refer to the video below for a step-by-step guide on completing traditional Windows enrollment. Ensure that the necessary configurations are set up before following the steps outlined in the video:
BYOD Enrollment Using QR Code
Prerequisites
- The server has to be downloaded and started.
- Must have been logged on to the server's Endpoint Management Portal.
- Install Entgra Android Agent on your android device.
- Optionally, Basic Concepts of Android Device Management will be beneficial as well.
Steps
Generate QR Code
- Go to Enroll Device section on Endpoint Management Portal.
- Select Android.
- Click Enroll Using QR.
- Add Username and select device ownership as BYOD.
- Click Generate QR Code.
Enroll Device as BYOD
- Open the Entgra Agent application on the Android mobile device.
- Click Continue after reading the Disclaimer that appears.
- In the screen that follows, click Enroll with QR Code.
- Scan QR code that is generated on the server.
- If you agree to the policy agreement that is shown next, click Agree to proceed.
- Click Activate on the device screen to enable Entgra Device Management Agent as a device admin app..
- Click Allow if you agree to the request for permissions for access to the device as indicated.
- Click Allow if you agree to using data usage monitoring to allow the server to check the data usage of the device.
- Allow the agent to change Do not Disturb status which is used to ring the device.
- Enter and confirm a PIN code, which is required by the administrator to perform any critical tasks with user consent. Then click Set PIN Code to complete the enrollment.
- Click Allow to enable Entgra IoT Remote Touch.
Video Tutorial for BYOD QR Enrollment
Refer to the video below for a step-by-step guide on completing traditional Windows enrollment. Ensure that the necessary configurations are set up before following the steps outlined in the video:
COPE Enrollment
COPE (corporately-owned personally-enabled) enrollment is ideal for devices where the organization gives out devices for its employees. With granular control over device data and security, and access to Android’s full suite of app management features, this type of enrollment offers comprehensive device management capabilities.
Some of the available features include setting the minimum password requirements on the device, ability to remotely wipe and lock the device, and setting up default responses to app permission requests. It is also possible to remotely install and/or remove apps with this type of enrollment.
Available enrollment modes for COPE enrollment:
COPE Manual Enrollment
Prerequisites
- The server has to be downloaded and started.
- Must have been logged on to the server's Endpoint Management Portal.
- Install ADB on your machine and enable USB Debugging on your Android device.
- Install Entgra Android Agent on your android device.
- Follow the Configurations section to set up necessary Android platform configurations.
- Optionally, Basic Concepts of Android Device Management will be beneficial as well.
Steps
Enable Device Owner
- The enrollment will be on hold until user enables the device owner. Enter the following command in the terminal or on the console to enable device owner.
Important
To execute ADB commands, first need to install ADB on your machine. To install ADB and enable USB debugging on your android device, please follow this documentation.
Enroll Device Manually
- Open the Entgra Agent application on your Android device.
- Click Continue after reading the Disclaimer that appears.
- On the next screen that appears next, click Manual Enrollment.
- Next, click COPE Enrollment in the screen that appears.
- Type in the server address which is the IP of the server and port as
8280. If you are using Entgra Cloud, type cloud server address here. Click Start Registration. - Type in the Username:
admin, Password:adminthen click Sign In. If you are an Entgra Cloud user, please do add your organization(tenant) name as well. - Click Allow if you agree to the request for permissions for access to the device as indicated.
- Click Allow if you agree to using data usage monitoring to allow the server to check the data usage of the device.
- Allow the agent to change Do not Disturb status which is used to ring the device.
- Click Allow to enable Entgra IoT Remote Touch.
Video Tutorial for COPE Manual Enrollment
Refer to the video below for a step-by-step guide on completing traditional Windows enrollment. Ensure that the necessary configurations are set up before following the steps outlined in the video:
COPE Enrollment Using QR Code (With Agent)
Prerequisites
- The server has to be downloaded and started.
- Must have been logged on to the server's Endpoint Management Portal.
- Install ADB on your machine and enable USB Debugging on your Android device.
- Install Entgra Android Agent on your android device. You can also install the Android Agent app using necessary adb commands. Example:
adb install filename.apk (adb install android-agent.apk) - Follow the Configurations section to set up necessary Android platform configurations.
- Optionally, Basic Concepts of Android Device Management will be beneficial as well.
Steps
Generate QR Code
- Go to Enroll Device section on Endpoint Management Portal.
- Select Android.
- Click Enroll Using QR.
- Add Username and select device ownership as COPE.
- Click Generate QR Code.
Scan QR Code
- Open the Entgra Agent application on the Android mobile device.
- Click Continue after reading the Disclaimer that appears.
- In the screen that follows, click Enroll with QR Code.
- Scan QR code that is generated on the server.
Enable Device Owner
The enrollment will be on hold until user enables the device owner. To enable device owner, you need to turn on USB Debugging on your Android device. Also need to install ADB on your machine.
- After enabling USB debugging and install ADB to your machine successfully, Enter the following command in the terminal or on the console to enable device owner.
Important
To execute ADB commands, first need to install ADB on your machine. To install ADB and enable USB debugging on your android device, please follow this documentation.
Grant Permissions
- Click Allow if you agree to the request for permissions for access to the device as indicated.
- Click Allow if you agree to using data usage monitoring to allow the server to check the data usage of the device.
- Allow the agent to change Do not Disturb status which is used to ring the device.
- Click Allow to enable Entgra IoT Remote Touch.
Video Tutorial for COPE QR Enrollment
Refer to the video below for a step-by-step guide on completing traditional Windows enrollment. Ensure that the necessary configurations are set up before following the steps outlined in the video:
COPE Enrollment Using QR Code After Factory Reset (Without Agent)
Prerequisites
- The server has to be downloaded and started.
- Must have been logged on to the server's Endpoint Management Portal.
- Follow the Configurations section to set up necessary Android platform configurations.
- Optionally, Basic Concepts of Android Device Management will be beneficial as well.
Steps
Generate QR Code
- Go to Enroll Device section on Endpoint Management Portal.
- Select Android.
- Click Enroll Using QR.
- Add Username and select device ownership as COPE.
- Click Settings icon to configure WIFI.
- Click Generate QR Code.
Enroll Device
- After switching on your new or factory resetted android device, tap the screen 7 times.
- It will turn on your device camera to scan the QR code.
- Follow the on-screen instructions to complete the enrollment process.
- Click Allow if you agree to the request for permissions for access to the device as indicated.
- Click Allow if you agree to using data usage monitoring to allow the server to check the data usage of the device.
- Allow the agent to change Do not Disturb status which is used to ring the device.
- Click Allow to enable Entgra IoT Remote Touch.
Video Tutorial for COPE Enrollment Using QR Code After Factory Reset (Without Agent)
Refer to the video below for a step-by-step guide on completing traditional Windows enrollment. Ensure that the necessary configurations are set up before following the steps outlined in the video:
Dedicated Device Enrollment (COSU/KIOSK)
The Dedicated type of Android Device Enrollment, also known as COSU (Corporately-Owned Single-Use) or KIOSK, is widely used with fully managed devices that serve a specific purpose. Examples of this type of usage include employee-facing device usage such as inventory management, field service management, transport, and logistics as well as customer-facing device usage like kiosks, digital signage, hospitality check-in, etc.
Some of the significant features of Dedicated devices are:
- Lock down devices to specific allow-listed apps
- Block users from escaping locked-down devices to enable other actions.
- Set lock screen restrictions
- Device sharing between multiple users (such as shift workers or public-kiosk users)
- Suspend over-the-air (OTA) system updates over critical periods by freezing the OS version.
- Remotely wipe and lock work data
- Automatic compliance enforcement
- Lock app(s) to screen
- Automatic compliance enforcement
- Distribute apps silently
Available enrollment modes for KIOSK enrollment:
KIOSK Enrollment Using QR Code (With Agent)
Prerequisites
- The server has to be downloaded and started.
- Must have been logged on to the server's Endpoint Management Portal.
- Install ADB on your machine and enable USB Debugging on your Android device.
- Install Entgra Android Agent on your android device. (You can also install the Android Agent app using necessary adb commands.Example:
adb install filename.apk (adb install android-agent.apk)) - Follow the Configurations section to set up necessary Android platform configurations.
- Optionally, Basic Concepts of Android Device Management will be beneficial as well.
Steps
Generate QR Code
- Go to Enroll Device section on Endpoint Management Portal.
- Select Android.
- Click Enroll Using QR.
- Add Username and select device ownership as COSU (KIOSK).
- Click Generate QR Code.
Scan QR Code
- Open the Entgra Agent application on the Android mobile device.
- Click Continue after reading the Disclaimer that appears.
- In the screen that follows, click Enroll with QR Code.
- Scan QR code that is generated on the server.
Enable Device Owner
The COSU(KIOSK) enrollment will be on hold until user enables the device owner. To enable device owner, you need to turn on USB Debugging on your Android device. Also need to install ADB on your machine.
- After enabling USB debugging and install ADB to your machine successfully, Enter the following command in the terminal or on the console to enable device owner.
Important
To execute ADB commands, first need to install ADB on your machine. To install ADB and enable USB debugging on your android device, please follow this documentation.
Grant Permissions
- If you agree to the policy agreement that is shown next, click Agree to proceed.
- Click Allow if you agree to the request for permissions for access to the device as indicated.
- Click Allow if you agree to using data usage monitoring to allow the server to check the data usage of the device.
- Allow the agent to change Do not Disturb status which is used to ring the device.
- Click Allow to enable Entgra IoT Remote Touch.
Video Tutorial for KIOSK Enrollment Using QR Code (With Agent)
Refer to the video below for a step-by-step guide on completing traditional Windows enrollment. Ensure that the necessary configurations are set up before following the steps outlined in the video:
KIOSK Enrollment Using QR Code After Factory Reset (Without Agent)
Prerequisites
- The server has to be downloaded and started.
- Must have been logged on to the server's Endpoint Management Portal.
- Follow the Configurations section to set up necessary Android platform configurations.
- Optionally, Basic Concepts of Android Device Management will be beneficial as well.
Steps
Generate QR Code
- Go to Enroll Device section on Endpoint Management Portal.
- Select Android.
- Click Enroll Using QR.
- Add Username and select device ownership as COSU (KIOSK).
- Click Settings icon to configure WIFI.
- Click Generate QR Code.
Enroll Device
- After switching on your new or factory resetted android device, tap the screen 7 times.
- It will turn on your device camera to scan the QR code.
- Follow the on-screen instructions to complete the enrollment process.
- Click Allow if you agree to the request for permissions for access to the device as indicated.
- Click Allow if you agree to using data usage monitoring to allow the server to check the data usage of the device.
- Allow the agent to change Do not Disturb status which is used to ring the device.
- Click Allow to enable Entgra IoT Remote Touch.
Video Tutorial for KIOSK Enrollment Using QR Code After Factory Reset (Without Agent)
Refer to the video below for a step-by-step guide on completing traditional Windows enrollment. Ensure that the necessary configurations are set up before following the steps outlined in the video:
Android Enterprise Enrollment
Android Enterprise allows EMMs to integrate with Google Play and make the enrollment and management of your mobile devices and apps much easier. Android enterprise offers some unique enrollment flows which allow enterprises to gain full control over devices. Two primary enrollment modes are:
Important
Before process Android Enterprise Enrollments, you must set up Android Enterprise Configurations under Android For Work section in Platform Configurations. Note that this step is necessary for aforementioned Android Enterprise Enrollment types.
Google Work Profile Enrollment
This mode is suitable for a Bring Your Own Device (BYOD) scenario. It creates a separate, secure space on the device known as the "work profile." The work profile keeps work-related apps and data isolated from the user's personal apps and data. Administrators can manage and secure the work profile without affecting the user's personal space.
Google Work Profile QR Enrollment Through Agent
After setting up Android Enterprise Configurations, you can perform a Google Work Profile enrollment via Entgra Android Agent. The enrollment process is almost similar to the BYOD QR Enrollment and it only differs from selecting Google Work Profile instead of BYOD from the ownership types dropdown.
Prerequisites
- The server has to be downloaded and started.
- Must have been logged on to the server's Endpoint Management Portal.
- Set up Android Enterprise Configurations
- Install Entgra Android Agent on your android device.
- Optionally, Basic Concepts of Android Device Management will be beneficial as well.
Steps
Generate QR Code
- Go to Enroll Device section on Endpoint Management Portal.
- Select Android.
- Click Enroll Using QR.
- Add Username and select device ownership as Google Work Profile.
- Click Generate QR Code.
Enroll Device
- Open the Entgra Agent application on the Android mobile device.
- Click Continue after reading the Disclaimer that appears.
- In the screen that follows, click Enroll with QR Code.
- Scan QR code that is generated on the server.
- If you agree to the policy agreement that is shown next, click Agree to proceed.
- Click Activate on the device screen to enable Entgra Device Management Agent as a device admin app..
- Click Allow if you agree to the request for permissions for access to the device as indicated.
- Click Allow if you agree to using data usage monitoring to allow the server to check the data usage of the device.
- Allow the agent to change Do not Disturb status which is used to ring the device.
- Enter and confirm a PIN code, which is required by the administrator to perform any critical tasks with user consent. Then click Set PIN Code to complete the enrollment.
- Click Allow to enable Entgra IoT Remote Touch.
Fully Managed Enrollment
Fully Managed type of enrollment is ideal for COPE (corporately-owned personally-enabled) devices where the organization gives out devices for its employees. With granular control over device data and security, and access to Android’s full suite of app management features, this type of enrollment offers comprehensive device management capabilities.
Some of the available features include setting the minimum password requirements on the device, ability to remotely wipe and lock the device, and setting up default responses to app permission requests. It is also possible to remotely install and/or remove apps with this type of enrollment.
Available enrollment modes for Fully Managed enrollment:
- Fully Managed QR through agent
- Fully Managed QR after factory reset
- Onboard Already Enrolled COPE Devices as Fully Managed
Fully Managed Enrollment Using QR Code (With Agent)
After setting up Android Enterprise Configurations, you can perform a Fully Managed Enrollment using QR code via Entgra Android Agent.
The enrollment process is almost similar to the COPE QR Enrollment and it only differs from selecting Fully Managed instead of COPE from the ownership types dropdown.
Prerequisites
- The server has to be downloaded and started.
- Must have been logged on to the server's Endpoint Management Portal.
- Install ADB on your machine and enable USB Debugging on your Android device.
- Install Entgra Android Agent on your android device. (You can also install the Android Agent app using necessary adb commands.Example:
adb install filename.apk (adb install android-agent.apk)) - Follow the Configurations section to set up necessary Android platform configurations.
- Optionally, Basic Concepts of Android Device Management will be beneficial as well.
Steps
Generate QR Code
- Go to Enroll Device section on Endpoint Management Portal.
- Select Android.
- Click Enroll Using QR.
- Add Username and select device ownership as Fully Managed.
- Click Generate QR Code.
Scan QR Code
- Open the Entgra Agent application on the Android mobile device.
- Click Continue after reading the Disclaimer that appears.
- In the screen that follows, click Enroll with QR Code.
- Scan QR code that is generated on the server.
Enable Device Owner
The Fully Managed enrollment will be on hold until user enables the device owner. To enable device owner, you need to turn on USB Debugging on your Android device. Also need to install ADB on your machine.
- After enabling USB debugging and install ADB to your machine successfully, Enter the following command in the terminal or on the console to enable device owner.
Important
To execute ADB commands, first need to install ADB on your machine. To install ADB and enable USB debugging on your android device, please follow this documentation.
Grant Permissions
- Click Agree in the screen that appears, if you agree to and accept the licence.
- Click Allow if you agree to the request for permissions for access to the device as indicated.
- Click Allow if you agree to using data usage monitoring to allow the server to check the data usage of the device.
- Allow the agent to change Do not Disturb status which is used to ring the device.
- Click Allow to enable Entgra IoT Remote Touch.
Fully Managed Enrollment Using QR Code After Factory Reset (Without Agent)
The enrollment process is almost similar to the COPE QR Enrollment After Factore Reset and it only differs from selecting Fully Managed instead of COPE from the ownership types dropdown.
Prerequisites
- The server has to be downloaded and started.
- Must have been logged on to the server's Endpoint Management Portal.
- Follow the Configurations section to set up necessary Android platform configurations.
- Optionally, Basic Concepts of Android Device Management will be beneficial as well.
Steps
Generate QR Code
- Go to Enroll Device section on Endpoint Management Portal.
- Select Android.
- Click Enroll Using QR.
- Add Username and select device ownership as Fully Managed.
- Click Settings icon to configure WIFI.
- Click Generate QR Code.
Enroll Device
- After switching on your new or factory resetted android device, tap the screen 7 times.
- It will turn on your device camera to scan the QR code.
- Follow the on-screen instructions to complete the enrollment process.
- Click Allow if you agree to the request for permissions for access to the device as indicated.
- Click Allow if you agree to using data usage monitoring to allow the server to check the data usage of the device.
- Allow the agent to change Do not Disturb status which is used to ring the device.
- Click Allow to enable Entgra IoT Remote Touch.
Onboard Already Enrolled COPE Devices as Fully Managed
If you have a device that is already onboarded as a COPE device, this device can be converted to a Fully managed device that works with Android enterprise.
- Go to the device that you need onboard as a fully managed device.
-
Click Create Account and click OK.
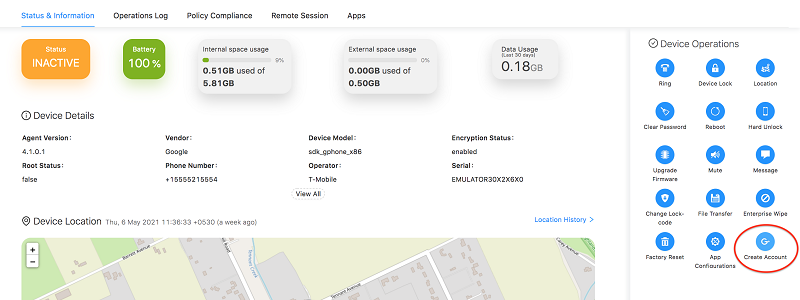
Account creation will take a few minutes.
Azure AD Integrated Enrollment - Just-In-Time Provisioning
Configure Azure AD
Steps
-
Sign in to Microsoft Azure Portal.
-
Go to App registrations and click New registration.

-
Provide a name for the application and a supported account type to use the application.
-
Then select Web from the drop down menu under Redirect URI section and provide endpoint management console URL in following format.
https://<hostname:port_no>/commonauth -
Click Register.

-
You will be redirected to a detailed page of the registered application. Make sure to save the Application (client) ID.

-
Next, go to the Certificates & secret section.
-
Click +New client secret, fill out the required fields of the drawer, and click Add at the bottom of the right-side drawer.

-
Make sure to save the Value and Secret ID in the Client secret tab.

-
Go back to Home and click Microsoft Entra ID.

-
Select Groups.

-
Click New group and fill the required information as follows;
Field Input Group type Security Group name Appropriate name for the group Membership type Assigned -
Then select and members to assign to the group.
-
Click Create.

-
You will now be redirected to a detailed page of created groups. Make sure to save the Object IDs of each group you created.

-
Then go back to Home and select App registration.
-
Go to the application you created and select Token configuration from the left menu.
-
Click Add optional claim. Select the token type as ID and select the claim as upn from the listed claims.
-
Then click Add.
-
Next, click Add groups claim. Select group type as Security group and expand the ID section there.

-
Select Group ID, and then select Emit groups as role claims check box.
-
Click Add.
-
Next, click API permission section from the left menu. There you can configure the profile scope permissions for the app you created.

-
Click Add a permission and select Microsoft Graph.
-
Then select Delegated permissions as the type of permissions that your application requires.
-
Now expand the OpenId permissions section and select email, openid and profile as necessary permissions.

-
Click Add permissions.

-
Then click Grant admin consent for
. 
-
Go back to the detailed view of your registered application and click Endpoints.
-
Copy and save the URL of OpenID Connect metadata document so that you can get the metadata information from there.

Configure External Identity Providers (IDPs)
Steps
-
Sign in to the Entgra UEM Server Management Console.
-
Expand the Identity section and click Add, under Identity Providers.

-
Fill out the following fields in each section with the correct information:
-
Basic Information
- Identity Provider Name
- Display Name
- Choose IDP Certificate Type (Select Use IDP JWKS endpoint)
- Identity Provider’s JWKS Endpoint (The JWKS URI can be found in the OpenID Connect metadata document)
-
Claim Configuration -> Basic Claim Configuration
- Select Define Custom Claim Dialect.
-
Then click Add Claim Mapping and add the following:
Identity Provider Claim URI Local Claim URI upn http://wso2.org/claims/displayName roles http://wso2.org/claims/role -
Then set User ID Claim URI as upn and Role Claim URI as roles.

-
Role Configuration
From here you can map your roles from External IDP end to the APIM end. Make sure to map at least one external role to the Internal/Subscriber role.
-
Click Add Role Mapping and add the following:
Identity Provider Role Local Role < Object ID > Internal/devicemgt-user < Object ID > Internal/subscriber < Object ID > < Customized role >
-
-
Federated Authenticators -> OAuth2/OpenID Connect Configuration
Add the following to the relevant fields:
Field Input Enable OAuth2/OpenIDConnect true Default true Client ID The Client ID of the app created for WSO2 APIM in the external IDP end Client Secret The generated secret Authorization Endpoint URL The authorization_endpoint in the OpenID Connect metadata document Token Endpoint URL The token_endpoint in the OpenID Connect metadata document Userinfo Endpoint URL The userinfo_endpoint in the OpenID Connect metadata document Token Endpoint URL Fill as “scope=openid” profile email 
-
Just-In-Time Provisioning:
- Select Always Provision to User Store Domain and then select PRIMARY from the dropdown.
- Next, select Provision silently.

-
Configure Service Providers(SPs)
-
Sign in to the Entgra UEM Server Management Console.
-
Expand the Identity section and click Add under Service Providers.

-
Fill out the following fields in each section with the relevant information:
-
Basic Information
- Service Provider Name
- Description
- Then click Register.

-
Select Use SP JWKS endpoint as the SP Certificate Type.
-
JWKS URI (The JWKS URI can be found in the OpenID Connect metadata document.)

-
Claim Configuration:
- Select Define Custom Claim Dialect under Claim mapping Dialect.
- Click Add Claim URI and fill out the details as follows:
Field Input Service Provider Claim upn Local Claim http://wso2.org/claims/displayName Requested Claim true - Select upn from the Subject Claim URI dropdown menu.

-
Inbound Authentication Configuration:
- Select Configure under OAuth2/OpenID Connect Configuration.

- Fill Callback URI as
https://localhost:9443/enroll-web-agent-ui-request-handler/jit-provision-callbackand then click Add.

- Now save the OAuth Client Key and OAuth Client Secret since these values will be needed for configuring the jit-config.xml.

-
Local & Outbound Authentication Configuration:
- Select Federated Authentication as the Authentication Type.
- Next, mark the check boxes for the following options:
- Skip Login Consent.
- Skip Logout Consent.
- Use user store domain in roles.

-
Add JIT Configuration
Steps
-
Navigate to the IOT_HOME/repository/conf directory and open the file named jit-config.xml.
-
Then, add the settings for your service provider as needed.
-
Now refer to the Configurations section to Add Service Provider Configuration.
iOS Enrollment Guide
This section describes how an iOS device can be enrolled to the UEM server. Before moving into iOS device enrollment it would be beneficial to understand the basic concepts of iOS related MDM concepts.
Prerequisites
- Prior to enrolling an iOS device, there are some configurations that need to be done on the server.
- If you have not requested for iOS plugin before, please contact Entgra to get a copy. If macOS support is needed in the plugin, please mention this in the description.(Although iOS is a supported device type of Entgra UEM server, by default it is not bundled with the server.)
- As mentioned in system requirements, maven is needed to install the plugin.
Install iOS plugin
iOS device plugin is not bundled with the server as out-of-the-box and as mentioned in prerequisites, it has to be requested from Entgra. A zip file containing the installable will be sent by Entgra and this can be installed with Maven.
Steps
- Copy the iOS plugin zip mentioned in the prerequisites to
IOT_HOMEfolder and extract. - Using command prompt, goto
IOT_HOME/ios-feature-deployer/folder. - Execute the following command mvn clean install
-f ios-feature-deployer.xml. - When the following question is asked Do you agree? (y,n) Type y and Enter to agree. Else, n to abort.
Run iOS Configurator
iOS configurator is a script designed to cut down certain manual configurations related to iOS.
Steps
- Using command prompt, goto IOT_HOME/ios-configurator/ folder
- Press Enter key to provide the default value and provide the following mandatory information with the server machine’s IP address:
- Common Name
- Server address
Customizing the iOS Bundle ID
If the bundle ID for the iOS agent is changed, the following changes have to be applied to the server configurations.
Steps
-
Open
iot-server.shfile inIOT_HOME/binfolder and search for key-Dagent-bundleand add the agent bundle ID as the value. -
Example
-Dagent-bundle=“org.wso2.carbon.emm.mdmagent”.
Create MDM APNS Certificate
Communication from server to device (OS MDM client) about new commands are delivered through Apple push notification service (APNS). To facilitate this, the UEM server needs to communicate with APNS servers and this requires a special certificate. In order to create an MDM APNS certificate, one of the following is needed,
- MDM vendor signing certificate which allow an EMM vendor to sign MDM APNS certificates for their customers
- Get an MDM vendor to provide you with an MDM APNS certificate
Steps to get Entgra to provide you with an MDM APNS certificate
-
This is the fastest approach and Entgra provides this server to valid customers. To do this, execute the following 2 commands on the commands prompt. The values provided when running these commands have no operation importance.
openssl genrsa -des3 -out customerPrivateKey.pem 2048 openssl req -new -key customerPrivateKey.pem -out customer.csr -
Keep the customerPrivateKey.pem file generate with above commands, secure along with the password used for private key. Email customer.csr file along with a description about the project details to contact@entgra.io to get a MDM APNS certificate. After an evaluation of the request, Entgra may send a file called plist_encoded
-
Go to the Apple Push Certificate Portal at https://identity.apple.com/pushcert/ and log in with an Apple ID. It is highly recommended not to use personal Apple IDs for this process and to create a separate Apple ID for the organization. This Apple ID is needed when these certificate needs to be renewed and failure to access this Apple ID in the future will result in having to re-enrol all the devices in production.
-
If you are trying to renew the certificate, click Renew.
- If not, Click Create Certificate and agree to the terms and conditions.
- Upload the encoded
plist_encodedfile you received via email from Entgra. -
Download the generated MDM signing certificate
(MDM_Certificate.pem). The MDM signing certificate is a certificate for 3rd party servers provided by Apple. -
Run the following command and note down the userID value in the output. This will later be indentified as the topic ID.
openssl x509 -in MDM_Certificate.pem -text -noout -
Run the following 2 commands,
openssl rsa -in customerPrivateKey.pem -out customerKey.pem cat MDM_Certificate.pem customerKey.pem > MDM_APNSCert.pem -
Open the MDM Apple Push Notification service (APNs) Certificate
(MDM_APNSCert.pem)and ensure that there is a line break between the contents of the two files.
Example: The content will look as follows:
—–END CERTIFICATE———-BEGIN RSA PRIVATE KEY—–
Therefore, add a line break to separate the 2 certificates after 5 - (dashes) so that the content will look like what’s shown below:
`-----END CERTIFICATE-----
-----BEGIN RSA PRIVATE KEY-----`
- Run the following command to convert the
MDM_APNSCert.pemfile to theMDM_APNSCert.pfxfile. You will need to provide a password when converting the file. `openssl pkcs12 -export -out MDM_APNSCert.pfx -inkey customerPrivateKey.pem -in MDM_APNSCert.pem'
Decide Your Enrollment Method
Before moving on to next steps, a decision needs to be made according to the features required for the business usecase. As mentioned previously, iOS and MacOS has an in-built MDM client which is capable of performing majority of management tasks. However the agent is needed, if the business requirement needs the following feature,
- Location tracking
- Ring the device
- Send a short notification message to device
If the above 3 features are not mandatory, please skip ahead to adding Platform Configurations section.
Create Agent APNS Certificate
This certificate is required to carry out operations on the device that need to be triggered via the iOS agent, such as ringing the device, getting the device location, and sending notifications or messages to the device. Therefore, if you are not installing the iOS agent on your devices, you do not need this certificate and this section can be skipped.
Prerequisites
- You have to be enrolled in the Apple Developer Program as an individual or an organization before starting the iOS server configurations.
- A valid distribution certificate that you obtained from Apple.
-
Clone the ios-agent repository to a preferred location.
git clone https://gitlab.com/entgra/ios-agent -
Open the emm-agent-iosfromX-Codeand follow the subsequent steps:-
Change the org.wso2.carbon.emm.mdmagent Bundle Identifier to a value prefered. Example:
org.<ORGANIZATION_NAME>.emm.ios.agent -
Select the development team, provisioning profile and sign certificate from Xcode.
-
If you are unsure of how to select the development team, or adding the provisioning profile or signing the certificate via Xcode, see the blog post on How to export “in-house” developed iOS app as an enterprise application.
-
-
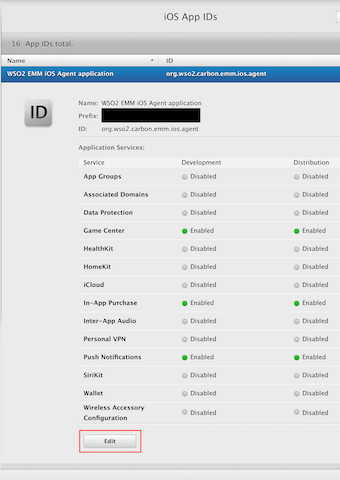
Log in to the Apple Developer program and follow the subsequent steps:
- Before you follow the steps, confirm that your machine is connected to the Internet and that Xcode has a valid developer account.
- Navigate to Certificates, IDs & Profiles that is under Identifiers. Click App IDs and see if the Bundle ID that you defined under Xcode is listed here.
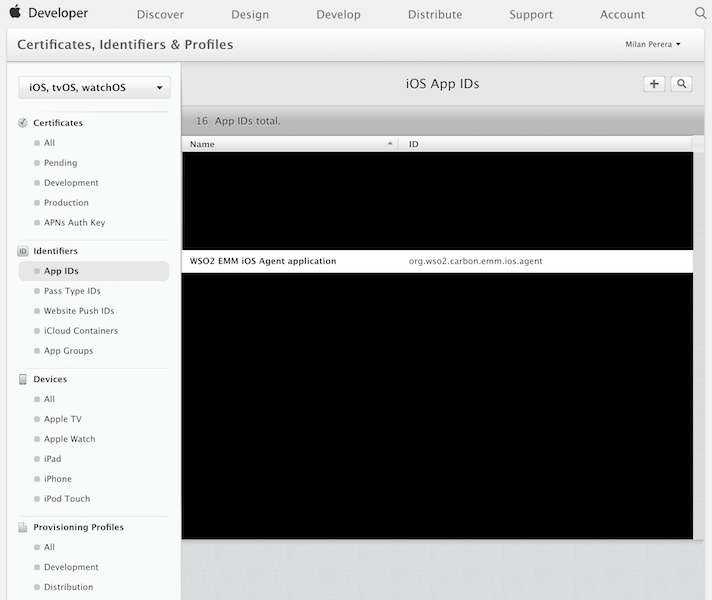
-
Click the Bundle ID, and click Edit.
-
Creating an APNs SSL certificate:
Step 1: Select Push Notifications to enable the setting.
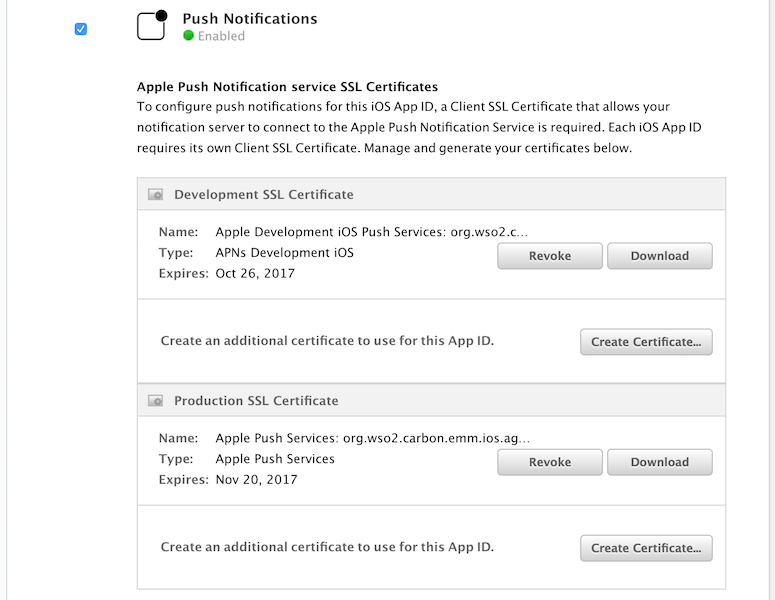
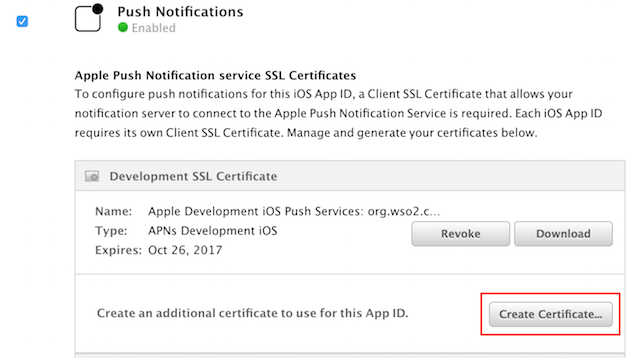
Once push notification is enabled, you are able to generate the development and production certificates.Step 2: To try out the create certificate use case, let us create a development SSL certificate. Please note that the development SSL certificate is created only as an example. You can create a production SSL certificate if you have registered with the Apple Developer Program as an Organization.
Click Create Certificate that is under Development SSL Certificate.
-
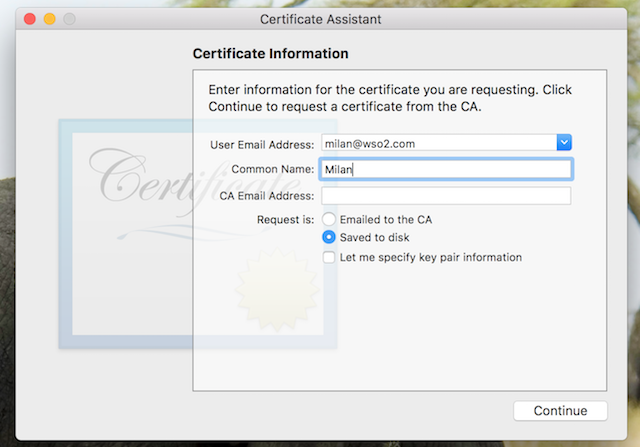
Creating a CSR file using the keychain access tool in the Mac OS:
Step 1: Launch the keychain access application.
Step 2: On the menu bar click KeyChain Access > Certificate Assistant > Request a Certificate from Certificate Authority.
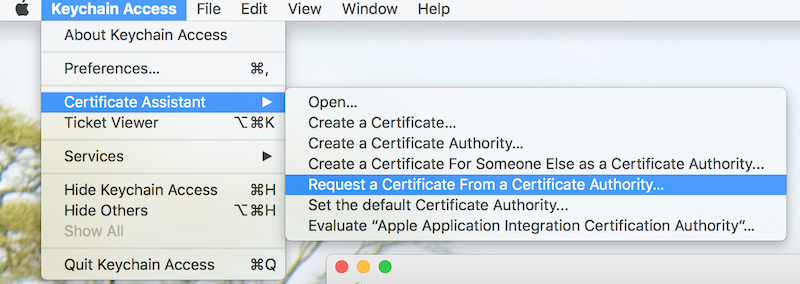
Step 3: Define the email address, common name, select Saved to disk, and click Continue. Example:
-
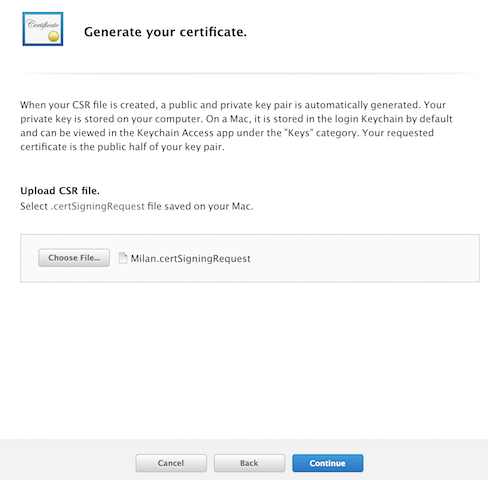
Go back to the Apple Developer Portal, upload the generated certificate, and click Continue.
-
Exporting the certificate to the pfx format.
8.1. Click Download to download the file.
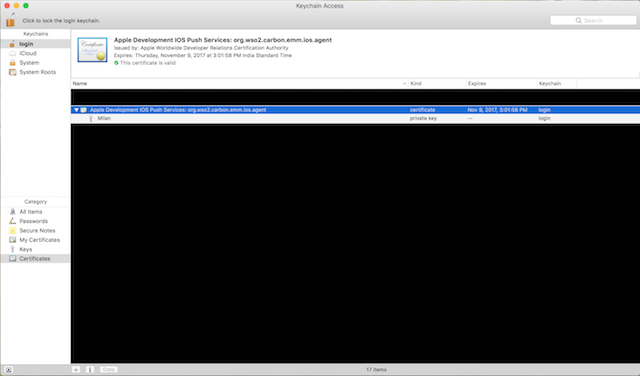
8.2. Double-click the downloaded file to open it with the Keychain access tool.
8.3. Right-click the certificate and select export.
8.4. Define the location where you wish to save the file and set a password for the exported file when prompted.
8.5. Rename the p12 extension of the file to pfx.
Add Platform Configurations
Before proceeding, note, if you require Apple DEP support, please complete Apple DEP configurations section first.
Steps
-
Log in to the device management console and Click > CONFIGURATION MANAGEMENT > PLATFORM CONFIGURATIONS > iOS Configurations and fill in the form with values you wish.
-
Use the generated MDM-APNS certificate for both the MDM certificate and the generated APNS certificate for the APNS certificate.
-
MDM Certificate: Upload the MDM APNS pfx file created
(MDM_APNSCert.pfx) -
MDM Certificate Password: Give the same password you gave when converting the MDM_APNS certificate from the pem to the pfx format.
-
MDM Certificate Topic ID: Give the topic ID of the certificate. If you are unsure of the topic ID, refer step 6 under generating the MDM APNS certificate.
-
APNS Certificate: If you are using Agent and completed Create agent APNS certificate section, please use that pfx. If not upload the MDM_APNSCert.pfx here as well APNS
-
Certificate Password: Give the same password you gave when converting the Agent APNS certificate to the pfx format. If Agent is not used, provide the same password as
MDM_APNSCert.pfx
-
Apple (iOS and MacOS) DEP Configurations
Device Enrollment Program (DEP) is a program provided by Apple to allow device management solutions to have control over corporate-owned devices. Let us take a look at what you need to do, to get started and understand why you need DEP.
Prerequisites
Apple server configurations must have been completed.
Benefits of using DEP
- Enables Zero Touch Provisioning (ZTP) for device enrollments for the convenience of IT administrators.
- Provides better control over iOS devices and provides the features described in the features section.
- Restrict the user from removing EMM Management from the device.
- Enrolling the Apple Device in the Enrollment Program
- The first step is to enroll your organization with Apple Device Enrollment Program (DEP) and link Entgra UEM Server’s EMM solution to your DEP portal. Follow the steps given below to enroll with DEP.
Steps
-
Generate a DEP Token to Link EMM with Apple.
- Now that the DEP account is created, EMM server must be made aware of this DEP account. In order to allow EMM server to talk to Apple DEP servers and link with the DEP account, a special server token has to be generated from Apple DEP portal and passed to EMM server.
Prerequisites
Download and install OpenSSL. Linux OS's have OpenSSL installed by default.
-
Linking the Entgra with Apple DEP
- You can configure the device startup settings (activation) of the iOS devices, to skip configurations or include additional configurations. This is done by creating profiles in Entgra UEM Server and assigning them to the devices.
-
Adding Devices to the Apple DEP Portal
- The Apple Device Enrollment Program (DEP) allows iOS devices purchased through the DEP program as well as those purchased outside of the program to be enrolled as supervised devices to a mobile device management system. You are required to add the devices to the Apple DEP portal to link the devices with the DEP system.
-
Adding Devices Purchased via DEP
-
Adding iOS Devices using the Apple Configurator
- The devices purchased outside DEP can be added manually to the DEP account. You need to plug in each device to a Mac and factory reset the device using THE Apple Configurator. Follow the steps given below:
Prerequisites
- Devices that have an OS that is iOS 11 or higher.
- Apple Configurator 2.5 or higher.
-
Creating and Assigning Activation Profiles to Devices
-
Enrolling DEP Devices
-
Please refer iOS DEP Device enrollment section.
Enroll iOS Device as BYOD without Agent
Prerequisites
- Server has to be downloaded and started.
- Must have been logged on to the server's Endpoint Management Portal.
- Click Enroll Device
(https://{IP}:{port}/devicemgt/device/enroll). - Click iOS.
- Scan the QR code that appear with a QR code scanning app or type
https://{IP}:{port}/ios-web-agent/enrollmentin safari browser.
If the Device is above iOS 12.2
(If you have installed OS updates after March 2019)
If the Device is bellow iOS 12.2
Enroll iOS Device as BYOD with Agent
Prerequisites
- Server has to be downloaded and started.
- Must have been logged on to the server's Endpoint Management Portal.
- Click Add Device
(https://{IP}:{port}/devicemgt/device/enroll). - Click iOS under DEVICE TYPES.
- Scan the QR code that appears with a QR code scanning app or type
https://IP:port/ios-web-agent/enrollmentin safari browser.
If the Device is above iOS 12.2
(If you have installed OS updates after March 2019)
If the Device is below iOS 12.2
iOS DEP Enrollment
iOS DEP Device Enrollment (with/without agent)
All you need to do is start up the iOS device that was given to you by your organization and your device will be enrolled with EMM as a DEP device.
If your organization has configured the DEP profile to prompt for your username and password, you need to enter the username and password that is used within the organization.
macOS Enrollment Guide
Enroll macOS Device Manually
Prerequisites
- The server has to be downloaded and started.
- Must have been logged on to the server's Endpoint Management Portal.
- Click iOS from DEVICE TYPES.
- Type
https://{IP}:{port}/ios-web-agent/enrollmentin safari browser.
Steps
-
Copy the URL of QR code to the browser of the mac OS device.
-
Click Enroll without agent.
-
Click Install UEM Server Certificate.
-
Open Key Chain Acess Application.
-
Open the downloaded UEM Server Certificate.
-
Set trust to Always trust for the downloaded UEM Server Certificate.
-
Click Next.
-
Type the Username:
admin, Password:adminthen click Sign in. -
Accept the Licence Agreement to continue.
-
You will be prompted to confirm the installation of the profile to the device. Then click Install to install the profile to the device.
-
You will be prompted to confirm the installation of the Mobile Device Management profile. Then click Install to install the Mobile Device Management profile to the device.
Windows Enrollment Guide
Note
- Before enrolling, make sure to set up Windows Server Configurations.
Windows Server Configuration
-
The Entgra UEM client sends requests to the Entgra UEM server through a Proxy Server. The Windows Entgra UEM protocol constructs a URI that uses the host name by appending the domain of the email address to the subdomain (enterpriseenrollment) for each device request. Therefore, you can either purchase a domain name or create a DNS entry in https://enterpriseenrollment. format.
-
For example, discover the Entgra UEM server by sending a request through: https://enterpriseenrollment/ENROLLMENTSERVER/Discovery. As the Entgra UEM server cannot create Windows service endpoints, it is advisable to use a proxy server between the device and the Entgra UEM server.
The following subsections are examples to guide you on configuring the proxy server for Windows. You can use any proxy server for this task but we recommend using Nginx as it is simple to try out.
Nginx Configuration
Note
A preferred server can be used as a proxy server between the device and the Entgra UEM server. The steps documented below are only an example of configuring the proxy server using NGINX, a known reverse proxy server.
Follow the steps given below to configure the proxy Server:
-
Install NGINX in your production environment. Refer to the following to install NGINX on a MAC or Ubuntu environment. NGINX installation guide
-
Get an SSL certificate. Make sure that the common name of the certificate you are getting matches the constructed URI.
a. In order to create the SSL certificate a file called openssl.cnf with the below content should be created:
[req] distinguished_name = req_distinguished_name req_extensions = v3_req [req_distinguished_name] countryName = SL countryName_default = SL stateOrProvinceName = Western stateOrProvinceName_default = Western localityName = Colombo localityName_default = Colombo organizationalUnitName = ABC organizationalUnitName_default = ABC commonName = dev.abc.com commonName_max = 64 [ v3_req ] # Extensions to add to a certificate request basicConstraints = CA:FALSE keyUsage = nonRepudiation, digitalSignature, keyEncipherment subjectAltName = @alt_names [alt_names] DNS.1 = dev.abc.com DNS.2 = enterpriseenrollment.dev.abc.comNote
Add the domain name needed to subject alternatives - DNS
b. Create the Private key.
c. Create a Certificate Signing Request (CSR). Press enter for every input. d. Sign the SSL Certificate.e. Create NGINX Windows configuration.openssl x509 -req -days 3650 -in server.csr -signkey server.key -out server.crt -extensions v3_req -extfile openssl.cnfI. Navigate to the /etc/nginx directory, create a folder named ssl, and add the CA certificate and the private key to this folder.
II. It is recommended to create a separate conf in NGINX to handle Windows configurations and add the below server config (i.e. /etc/nginx/conf.d/window.conf) with the details of the SSL certificate and the Windows endpoints as explained below.
f. Configure the SSL certificate details.server { listen 443 ssl; server_name enterpriseenrollment.dev.abc.com; ssl_certificate /etc/nginx/ssl/server.crt; ssl_certificate_key /etc/nginx/ssl/server.key; access_log /var/log/nginx/windows/http/access.log; error_log /var/log/nginx/windows/http/error.log; location /EnrollmentServer/Discovery.svc { if ($request_method = GET) { access_log /var/log/nginx/windows/ok/access.log; return 200; } proxy_set_header X-Forwarded-Host $host:$server_port; proxy_set_header X-Forwarded-Server $host; proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for; proxy_pass https://<SERVER_IP>:8243/api/device-mgt/windows/v1.0/discovery/post; proxy_http_version 1.1; } location /ENROLLMENTSERVER/PolicyEnrollmentWebservice.svc { proxy_set_header X-Forwarded-Host $host:$server_port; proxy_set_header X-Forwarded-Server $host; proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for; proxy_pass https://<SERVER_IP>:8243/api/device-mgt/windows/v1.0/certificatepolicy/xcep/; proxy_http_version 1.1; } location /ENROLLMENTSERVER/PolicyEnrollmentWebserviceOnPremise.svc { proxy_set_header X-Forwarded-Host $host:$server_port; proxy_set_header X-Forwarded-Server $host; proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for; proxy_set_header content-type "application/xml"; proxy_pass https://<SERVER_IP>:8243/api/device-mgt/windows/v1.0/certificatepolicy/xcep/onpremise; proxy_http_version 1.1; } location /ENROLLMENTSERVER/DeviceEnrollmentWebservice.svc { proxy_set_header X-Forwarded-Host $host:$server_port; proxy_set_header X-Forwarded-Server $host; proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for; proxy_pass https://<SERVER_IP>:8243/api/device-mgt/windows/v1.0/deviceenrolment/wstep/; proxy_http_version 1.1; } location /ENROLLMENTSERVER/Win10DeviceEnrollmentWebservice.svc { proxy_set_header X-Forwarded-Host $host:$server_port; proxy_set_header X-Forwarded-Server $host; proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for; proxy_pass https://<SERVER_IP>:8243/api/device-mgt/windows/v1.0/deviceenrolment/enrollment; proxy_http_version 1.1; } location /ENROLLMENTSERVER/Win10DeviceEnrollmentWebserviceOnPremise.svc { proxy_set_header X-Forwarded-Host $host:$server_port; proxy_set_header X-Forwarded-Server $host; proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for; proxy_set_header content-type "application/xml"; proxy_pass https://<SERVER_IP>:8243/api/device-mgt/windows/v1.0/deviceenrolment/enrollment/onpremise; proxy_http_version 1.1; } location /Syncml/initialquery { proxy_set_header X-Forwarded-Host $host:$server_port; proxy_set_header X-Forwarded-Server $host; proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for; proxy_pass https://<SERVER_IP>:8243/api/device-mgt/windows/v1.0/syncml/devicemanagement/request/; proxy_http_version 1.1; } location /devicemgt { proxy_set_header X-Forwarded-Host $host:$server_port; proxy_set_header X-Forwarded-Server $host; proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for; proxy_set_header Authorization ""; proxy_pass https://<SERVER_IP>:8243/api/device-mgt/windows/v1.0/management/devicemgt/pending-operations; proxy_http_version 1.1; } location /api/device-mgt/windows/v1.0/configuration/license { proxy_set_header X-Forwarded-Host $host:$server_port; proxy_set_header X-Forwarded-Server $host; proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for; proxy_pass https://<SERVER_IP>:8243/api/device-mgt/windows/v1.0/configuration/license; proxy_http_version 1.1; } location /windows-web-agent { proxy_set_header X-Forwarded-Host $host:$server_port; proxy_set_header X-Forwarded-Server $host; proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for; proxy_pass https://<SERVER_IP>:9443/windows-web-agent; proxy_http_version 1.1; } location /enroll-web-agent-ui-request-handler { proxy_set_header X-Forwarded-Host $host:$server_port; proxy_set_header X-Forwarded-Server $host; proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for; proxy_set_header Host $http_host; proxy_pass https://<SERVER_IP>:9443/enroll-web-agent-ui-request-handler; proxy_http_version 1.1; } location /api/device-mgt/windows/v1.0/federated/authentication { proxy_set_header X-Forwarded-Host $host:$server_port; proxy_set_header X-Forwarded-Server $host; proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for; proxy_pass https://<SERVER_IP>:9443/api/device-mgt/windows/v1.0/federated/authentication; proxy_http_version 1.1; } }You need to configure the following properties:server { listen 443 ssl; server_name enterpriseenrollment.dev.abc.com; ssl_certificate /etc/nginx/ssl/server.crt; ssl_certificate_key /etc/nginx/ssl/server.key;Property Description Example server_name Define the common name of the certificate enterpriseenrollment.dev.abc.com ssl_certificate Define where you saved the SSL certificate /etc/nginx/ssl/server.crt ssl_certificate_key Define where you saved the private key of the certificate /etc/nginx/ssl/server.key g. Configure the Windows endpoints.
Note
- The GATEWAY_HTTPS_PORT used by default in Entgra UEM for device management is 8243.
- https://SERVER_IP:GATEWAY_HTTPS_PORT
- https://SERVER_IP:8243
- The MANAGEMENT_HTTPS_PORT used by default in Entgra UEM for device management is 9443.
- https://SERVER_IP:MANAGEMENT_HTTPS_PORT
- https://SERVER_IP:9443
Example of both ports used:
location /ENROLLMENTSERVER/PolicyEnrollmentWebservice.svc { proxy_set_header X-Forwarded-Host $host:$server_port; proxy_set_header X-Forwarded-Server $host; proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for; proxy_pass https://<SERVER_IP>:8243/api/device-mgt/windows/v1.0/certificatepolicy/xcep/; proxy_http_version 1.1; } location /windows-web-agent { proxy_set_header X-Forwarded-Host $host:$server_port; proxy_set_header X-Forwarded-Server $host; proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for; proxy_pass https://<SERVER_IP>:9443/windows-web-agent; proxy_http_version 1.1; }Property Description Location This property specifies the "/" prefix that needs to be compared with the URI sent from the request. For more information, see the NGINX documentation. Proxy_pass Define the respective Windows endpoint. Proxy_set_header Required headers to configure Windows endpoints for reverse proxying. - The GATEWAY_HTTPS_PORT used by default in Entgra UEM for device management is 8243.
Enroll Windows Device
This section describes the types of enrollment available for Windows Devices and how to enroll a Windows device to Entgra UEM portal. The available enrollment types are:
- Traditional Enrollment (BYOD)
- Windows Azure AD Integrated Enrollment
- Windows Bulk Enrollment
- Windows Autopilot
Traditional Enrollment (BYOD)
This method enables you to enroll a Windows device as BYOD through Windows settings, making it suitable for managing devices with minimal restrictions.
Prerequisite
Before enrolling, make sure to set up Windows Server Configurations in the Configurations section.
Steps
-
On the Windows device, navigate to Windows Settings > Accounts > Access work or school.
-
Under Related settings, click Enroll only in device management.

-
In the pop-up window, enter
admin@<EMAIL_DOMAIN>as the email address (e.g., admin@dev.abc.com), and click Next.
-
(Optional) Enter the MDM Server URL as
EnterpriseEnrollment.<EMAIL_DOMAIN>(e.g., EnterpriseEnrollment.dev.abc.com), and click Next. -
Enter your username and password, then click Log in to authenticate with the Entgra UEM Server.

-
Review and accept the license agreement to complete the enrollment process.

-
Upon successful enrollment, the connected server will appear under Access work or school with the relevant management information.

-
Log in to the Endpoint Management portal and navigate to the All Devices page. The enrolled Windows device will appear in the device list.
Video Tutorial for Traditional Enrollment
Refer to the video below for a step-by-step guide on completing traditional Windows enrollment. Ensure that the necessary configurations are set up before following the steps outlined in the video:
Windows Azure AD Integrated Enrollment
Windows Azure Active Directory (AD) enrollment enables the use of Microsoft Azure AD account credentials for enrolling Azure AD registered and joined devices into the Entgra UEM server. During this process, the corresponding Azure AD user is automatically provisioned on the UEM server.
Prerequisite
- Before enrolling, make sure to set up Windows Server Configurations in the Configurations section.
- Subsequently, refer to the Entra ID (Azrure AD) Configurations for Windows Enrollment for setup your Azure AD environment.
In Azure AD-based enrollment, two types of enrollments are available:
-
Azure AD Registered Devices (BYOD): This enrollment type is for Bring Your Own Device (BYOD) scenarios, where personal devices are registered with Azure Active Directory for secure access to organizational resources.
-
Azure AD Joined Devices (COPE): This enrollment type is designed for Corporate-Owned, Personally Enabled (COPE) devices, where devices are joined to Azure Active Directory, providing stronger management and security controls for organizational use.
Enroll Azure AD Registered devices (BYOD)
-
Azure AD registered enrollments are intended for Bring Your Own Device (BYOD) scenarios, allowing Windows devices to be enrolled through Windows settings. This method is suitable for managing devices with minimal restrictions.
-
The enrollment process can be initiated through, either: Windows Settings > Accounts > Access work and school > Connect > Enter Azure AD credentials or during the initial setup of a Windows device, known as Out-of-Box Experience (OOBE).
-
In this enrollment type, the local device user retains administrative privileges and can disconnect from the Mobile Device Management (MDM) system at any time.
Steps
-
On the Windows device, navigate to Windows Settings > Accounts > Access work or school.
-
Click on + Connect.

-
Enter your email address and click Next.

-
Enter your password and click Sign in.
-
Review and accept the license agreement to complete the enrollment process.

-
In the Use Windows Hello with your account window, click OK.

-
Set a password or PIN, then click OK.

-
In the Almost done window, click Next.

-
Verify that the account has been added by checking Access work or school. The account should now be visible.

-
Log in to the Endpoint Management portal and navigate to the All Devices page. The enrolled Windows device will be listed in the device table.
Video Tutorial for Azure AD Registered Device Enrollment
Refer to the video below for a step-by-step guide on completing traditional Windows enrollment. Ensure that the necessary configurations are set up before following the steps outlined in the video:
Enroll Azure AD Joined devices (COPE)
-
Azure AD joined enrollments are designed for Corporate-Owned, Personally Enabled (COPE) scenarios.
-
Enrollment can be initiated either through Windows Settings > Accounts > Access work and school > Connect > Join this device to Azure Active Directory > Enter Azure AD credentials or during the initial setup of a Windows device, known as Out-of-box experience (OOBE).
-
If the enrollment occurs after OOBE, the local device user will have administrative privileges, allowing them to disconnect from the MDM at any time.
-
To enroll the user without granting local device user admin privileges, supported enrollments include OOBE enrollment using a provisioning package (.ppkg) created with an Azure AD bulk token or using Windows Autopilot. More details.
Steps
-
On the Windows device, navigate to Windows Settings > Accounts > Access work or school.
-
Click on + Connect.

-
Click on Join this device to Microsoft Entra ID under Alternate actions.

-
Enter the email address and click Next.

-
Enter password and click Sign in.

-
Review and accept the license agreement to complete the enrollment process.

-
Click Done in the You’re all set window.

-
Verify that the account has been added by checking Access work or school. The account should now be visible.

-
Log in to the Endpoint Management portal and navigate to the All Devices page. The enrolled Windows device will be listed in the device table.
Video Tutorial for Azure AD Joined Device Enrollment
Refer to the video below for a step-by-step guide on completing traditional Windows enrollment. Ensure that the necessary configurations are set up before following the steps outlined in the video:
Windows Bulk Enrollment
Through provisioning packages, Windows devices can be enrolled in bulk directly to the UEM server either in BYOD mode or, by utilizing an Azure AD bulk token to generate a provisioning package. They can also be enrolled in COPE mode if the package is applied during the OOBE.
Bulk enrollments will be done using provisioning packages and to create a provisioning package, it needs to be done on a Windows device using the Windows Configuration Designer tool. More details.
In bulk enrollment, two types of enrollment methods are available:
-
Bulk Enrollment Directly to UEM Server (BYOD): This method is used for Bring Your Own Device (BYOD) scenarios, where devices are enrolled in bulk directly to the UEM server without requiring additional integrations.
-
Bulk Enrollment with Azure AD Integration (COPE): This method is for Corporate-Owned, Personally Enabled (COPE) devices, where bulk enrollment is integrated with Azure Active Directory, providing enhanced management and security capabilities.
Prerequisites
- Before enrolling, make sure to set up Windows Server Configurations in the Configurations section.
- Subsequently, refer to the Entra ID (Azrure AD) Configurations for Windows Enrollment for setup your Azure AD environment. (This is applicable only for bulk enrollment with Azure AD integration)
Bulk Enrollment Directly to UEM Server (BYOD)
-
Bulk enrollments can be performed using the on-premises authentication device enrollment flow through Windows settings to enroll Windows devices as BYOD.
-
This process enables the bulk enrollment of devices to a designated existing user on the UEM server.
-
To generate a provisioning package for this enrollment type, the credentials of the intended user, to whom all devices will be enrolled, are required, along with the Windows enrollment URLs.
-
Please refer to the relevant documentation for detailed information on enrolling Windows devices as BYOD using the bulk enrollment method. Bulk enrollment using Windows Configuration Designer
Steps
-
Install Windows Configuration Designer (WCD) from the Microsoft Store.
-
Open the WCD tool.
-
Select Advanced Provisioning.

-
Enter a project name and select Next.

-
Select All Windows editions, since Provisioning CSP is common to all Windows editions, then select Next.

-
Skip Import a provisioning package (optional) and select Finish.

-
Expand Runtime settings > Workplace.

-
Select Enrollments, enter a value in UPN, and then select Add.
Note
The UPN is a unique identifier for the enrollment. For bulk enrollment, this UPN must be an existing user in the UEM server with the permission to enroll devices, such as
admin@entgra.io(where admin is the username and entgra.io is the tenant domain-for more details refer to Manage Tenants section).
-
On the left navigation pane, expand the UPN and then enter the information for the rest of the settings for the enrollment process. Here's the list of available settings:
- UPN: Username with tenant domain.
eg: admin@entgra.io - AuthPolicy: OnPremise
- DiscoveryServiceFullUrl: https://ENTERPRISE_ENROLLMENT_URL/EnrollmentServer/Discovery.svc
- EnrollmentServiceFullUrl: https://ENTERPRISE_ENROLLMENT_URL/ENROLLMENTSERVER/Win10DeviceEnrollmentWebserviceOnPremise.svc
- PolicyServiceFullUrl: https://ENTERPRISE_ENROLLMENT_URL/ENROLLMENTSERVER/PolicyEnrollmentWebserviceOnPremise.svc
- Secret: Password of the user mentioned in UPN.
Note
ENTERPRISE_ENROLLMENT_URL is the server_name mentioned in the Windows Server Configurations or the domain name that the Entgra UEM server is hosted on.
For detailed descriptions of these settings, see Provisioning CSP. Here's the screenshot of the WCD at this point.

- UPN: Username with tenant domain.
-
Configure the other settings, such as the Wi-Fi connections so that the device can join a network before enrolling to the Entgra UEM server (for example, Runtime settings > ConnectivityProfiles > WLANSetting).
-
After adding all the settings, select Save on the File menu.
-
On the main menu, select Export > Provisioning package.

-
Enter the values for your package and specify the package output location.



-
Select Build.

-
Click Finish.

-
Apply the package to some test devices and verify that they work. For more information, see Apply a provisioning package.
-
Apply the package to your devices.
Bulk Enrollment with Azure AD Integration (COPE)
-
A provisioning package can be created using Azure AD credentials from a user who has cloud admin privileges on Azure.
-
In this enrollment scenario, a temporary user is created within the Azure tenant, and mapped to the bulk token generated during package creation. More details.
-
If the provisioning package is applied during OOBE the device will be enrolled in COPE mode otherwise if the package was applied on an already set-up device (post-OOBE) then the local device user will have admin privileges. More details.
Steps
-
Install Windows Configuration Designer (WCD) from the Microsoft Store.
-
Open the WCD tool.
-
Select Provision desktop devices.

-
A New project window opens where you specify the following information:
- Name: A name for your project
- Project folder: Save location for the project
- Description: An optional description of the project

-
Enter a unique name for your devices. Names can include a serial number (%SERIAL%) or a random set of characters. Optionally, you can also enter a product key if you are upgrading the edition of Windows, configure the device for shared use, and remove pre-installed software.

-
Optionally, you can configure the Wi-Fi network devices connect to when they first start. If the network devices aren't configured, a wired network connection is required when the device is first started.

-
Select Enroll in Azure AD, enter a Bulk Token Expiry date, and then select Get Bulk Token. The token validity period is 180 days.
-
Provide your Microsoft Entra credentials to get a bulk token.

-
In the Stay signed in to all your apps page, select No, sign in to this app only.
-
Click Next when Bulk Token is fetched successfully.
-
Optionally, you can Add applications and Add certificates. These apps and certificates are provisioned on the device.
-
Optionally, you can password-protect your provisioning package. Click Create.

Windows Autopilot
Windows Autopilot simplifies the device lifecycle by streamlining deployment and configuration processes. Devices can be enrolled directly from the out-of-the-box experience (OOBE) without IT intervention. With an internet connection and Azure Active Directory credentials, users can enroll devices in just a few simple steps.
Prerequisites
- Before enrolling, make sure to set up Windows Server Configurations in the Configurations section.
- Subsequently, refer to the Entra ID (Azrure AD) Configurations for Windows Enrollment for setup your Azure AD environment.
Steps
-
Create an Autopilot deployment profile in Microsoft Intune. For detailed instructions, refer to the Autopilot profiles documentation.
-
Assign a device or user group to the deployment profile. For instructions on assigning a dynamic group, see this guide.
-
During OOBE, open Command Prompt or PowerShell (press Shift + F10) and run the following commands:
PowerShell.exe -ExecutionPolicy Bypass Install-Script -name Get-WindowsAutopilotInfo -Force Set-ExecutionPolicy -Scope Process -ExecutionPolicy RemoteSigned Get-WindowsAutopilotInfo -OnlineNote
- If the device is using Wi-Fi instead of Ethernet, use the following command to view available networks:
Start ms-availablenetworks: - For more details on network issues during pre-provisioning, refer to this Autopilot network error guide.
- If the device is using Wi-Fi instead of Ethernet, use the following command to view available networks:
-
After executing the last command a sign up window will come up. Use the credentials of a Cloud Administrator to successfully register the device to Autopilot servers.

-
If the assigned group is not dynamic, once the device is successfully imported, go to the Azure AD portal and manually assign the device to the group that was initially linked to the deployment profile.
-
Restart the device by running the following command in Command Prompt or PowerShell:
restartorshutdown /s /t 0 -
Once the Autopilot registration is successful after a restart, the device will ask for a sign in. During this step everything is configured for the end user to start enrolling this device, the user should enter their Azure AD credentials during this step and Click on Next.
Important
The user credentials should not be the cloud administrator’s at this stage

-
Review and accept the license agreement to complete the enrollment process.

-
In the Use Windows Hello with your account window, click OK.

-
Set a password or PIN, then click OK.

-
Click Done in the You’re all set window.

-
Verify that the account has been added by checking Access work or school. The account should now be visible.

Entgra Windows Device Management Agent Deployment
Important
Entgra Windows Device Management Agent is essential for managing Windows OS updates, enabling screen sharing, and publishing applications.
The Entgra Windows Agent consists of two components which should be installed separately.
- Desktop App (.appx): This is a UWP application that handles user interactions
- Background Service (.msi): This service runs in the background to manage tasks related to device communication and system functions
The installation process can be completed in two ways:
- Install through platform configurations on the Entgra Endpoint Management portal (Recommended)
- Install through the Entgra App Publisher and App Store
Install through Entgra Endpoint Management portal (Recommended)
Install through Entgra Endpoint Management portal (Recommended)
- Log in to the Endpoint Management Portal.
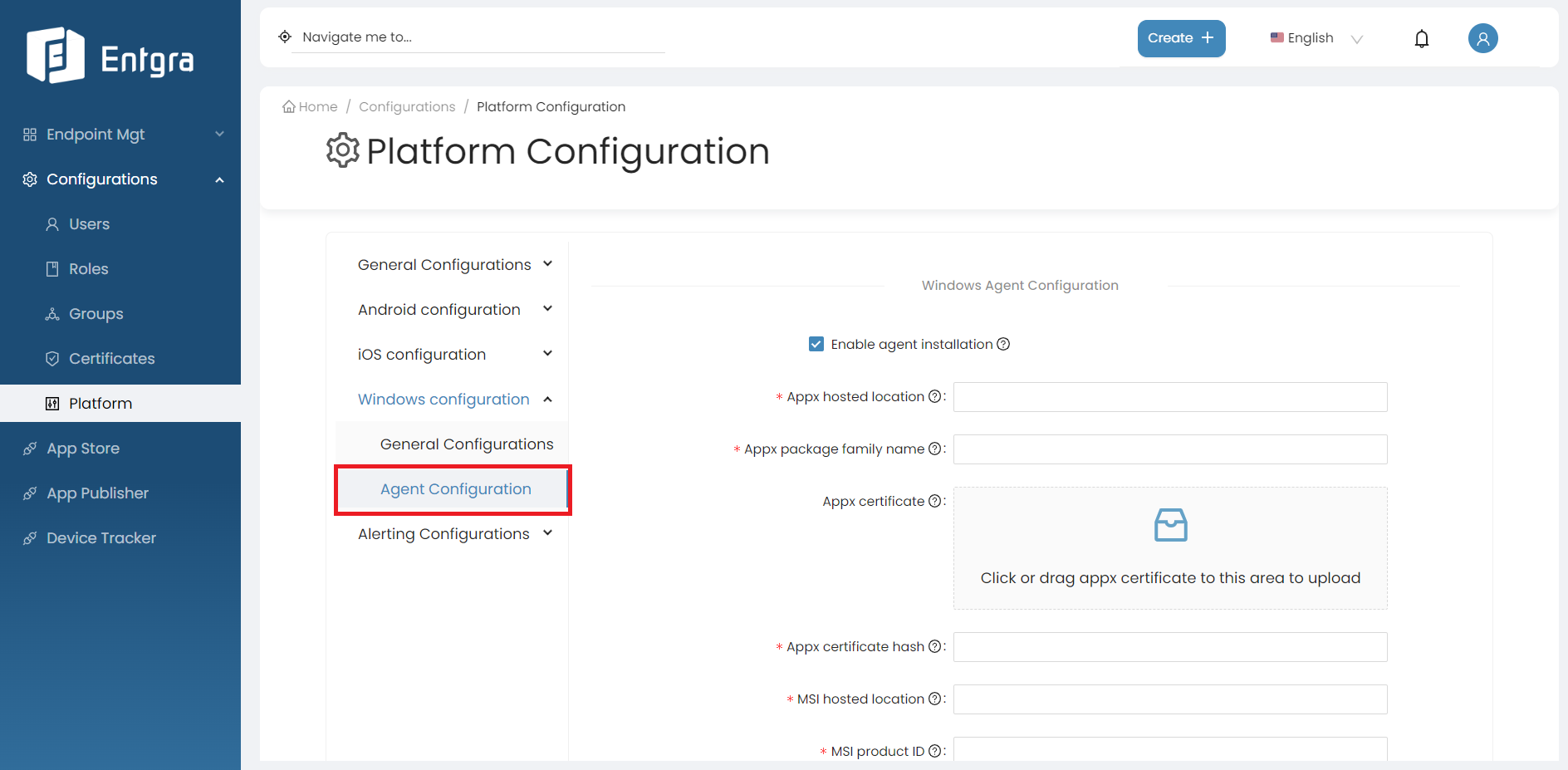
- Navigate to Platform Configurations and select Windows Configurations.
-
Click on Agent Configurations.
-
Enable agent installation and provide the required details as follows.
Field Input Appx hosted location Desktop App (APPX) Appx package family name WindowsAgent_gb3rxaghv37ag Appx certificate windows-agent-cert.cer Appx certificate hash 30A30C663FF96DD848F849A1183B7379F6F9CB4B MSI hosted location Background Service (MSI) MSI product ID 327DB9A7-6CAE-452C-8148-011BB1E1DDA9 MSI file hash 546D443C5443DAC6642DC3BF3B656108D88B20DB7713092CEE6433FB602CDB13
After applying the necessary configurations, any devices that are enrolled or re-enrolled will automatically receive an agent installation command.
Install through Entgra App Publisher and Store
Install through Entgra App Publisher and Store
Important
This approach is recommended only if re-enrolling devices is not possible or if a new version of the Entgra Windows Agent is available.
Step 1: Publish Entgra Windows Agent Desktop App (APPX)
- Log in to the Entgra App Publisher Portal.
- Click Add New App + on the navigation bar.
- Select Enterprise App.
- Enter the required details at each step as follows. Refer to Publish Enterprise App for more details.
In the Application stage,
- Select Device Type as Windows.
- Enter the App name and App description.
- Visible roles is not mandatory.
- Choose relevant categories/tags.
- Click on Add Release.
In the Uploads stage,
- Upload the Desktop App (APPX) file.
- Select the relevant icons and screenshots.
In the Release stage,
- Enter the details as follows:
- Package Name: WindowsAgent_gb3rxaghv37ag
- Version: 1.0.0.0
- Package Url: Desktop App (APPX)
- Dependency Package Url: This is not mandatory
- Certificate Hash: 30A30C663FF96DD848F849A1183B7379F6F9CB4B
- Appx certificate: windows-agent-cert.cer
- Add a release type and description.
- Supported OS Versions: 10 to 11.
- META DATA is not mandatory.
- Select Directly move the release to published state and click Submit.
Step 2: Publish Entgra Windows Agent Background Service App (MSI)
- Log in to the Entgra App Publisher Portal.
- Click Add New App + on the navigation bar.
- Select Enterprise App.
- Enter the required details at each step as follows. Refer to Publish Enterprise App for more details.
In the Application stage,
- Select Device Type as Windows.
- Enter the App name and App description.
- Visible roles is not mandatory.
- Choose relevant categories/tags.
- Click on Add Release.
In the Uploads stage,
- Upload the Agent Background Service App (MSI) file.
- Select the relevant icons and screenshots.
In the Release stage,
- Enter the details as follows:
- Package Name: Entgra Agent Service
- Version: 1.0.0
- Product ID: 327DB9A7-6CAE-452C-8148-011BB1E1DDA9
- Content URI: Background Service (MSI)
- File Hash: 546D443C5443DAC6642DC3BF3B656108D88B20DB7713092CEE6433FB602CDB13
- Add a release type and description.
- Supported OS Versions: 10 to 11.
- META DATA is not mandatory.
- Select Directly move the release to published state and click Submit.
Step 3: Install Entgra Windows Agent Desktop App (APPX)
- Refer to the App Installation guide to install the Windows Agent Desktop App (APPX).
Step 3: Install Entgra Windows Agent Background Service App (MSI)
- Refer to the App Installation guide to install the Windows Agent Background Service App (MSI).
Enrollment Issue Diagnosis
You may encounter issues while trying to enroll your Windows devices to the server. There are tools that can help diagnose the enrollment or device management issue accurately for Windows devices managed by the MDM server. By using these tools, you can examine the MDM logs collected from the desktop to determine the root cause of the issue.
Diagnose MDM Failure in Windows 10
Reference: Diagnose MDM failures in Windows 10
Follow the steps below to download the MDM Diagnostic Information log from Windows PC:
- Enroll the device to the MDM server.
- Go to Settings > Accounts > Access Work or School.
- Click on the Info button of the account.
- At the bottom of the page, select the Create Report button under Advanced Diagnostic Report section.
- Click Export.
-
Go to C:/Users/Public/Documents/MDMDiagnostics to see the exported report. That report contains detailed information on the areas given below:
- Device info
- Connection info
- Device management account
- Certificates
- Enrolled configuration sources and target resources
- Managed policies
- GPCSEWreapper policies
- Blocked grouped policies
- Unmanaged policies
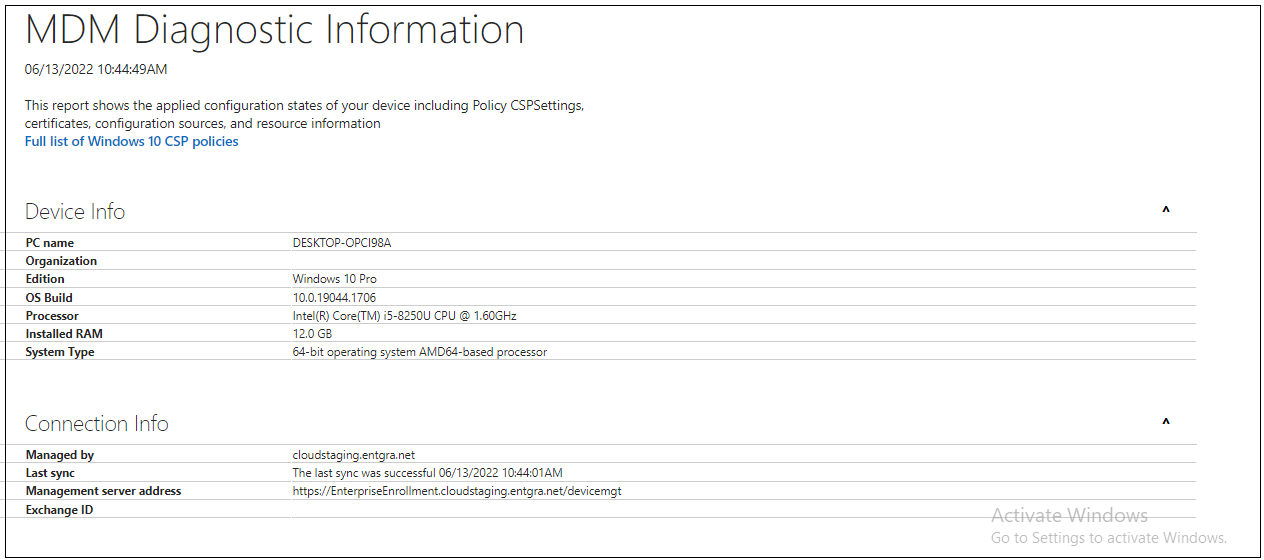
Diagnose MDM Failures using Event Viewer
Microsoft Windows Server Event Viewer is a monitoring tool that shows a log of events that can be used to troubleshoot issues on a Windows-based system. Follow the steps below to open the Event View:
-
Click Start > Control panel > System and security > Administrative tools > Event viewer Or Right click Start and select Event viewer.
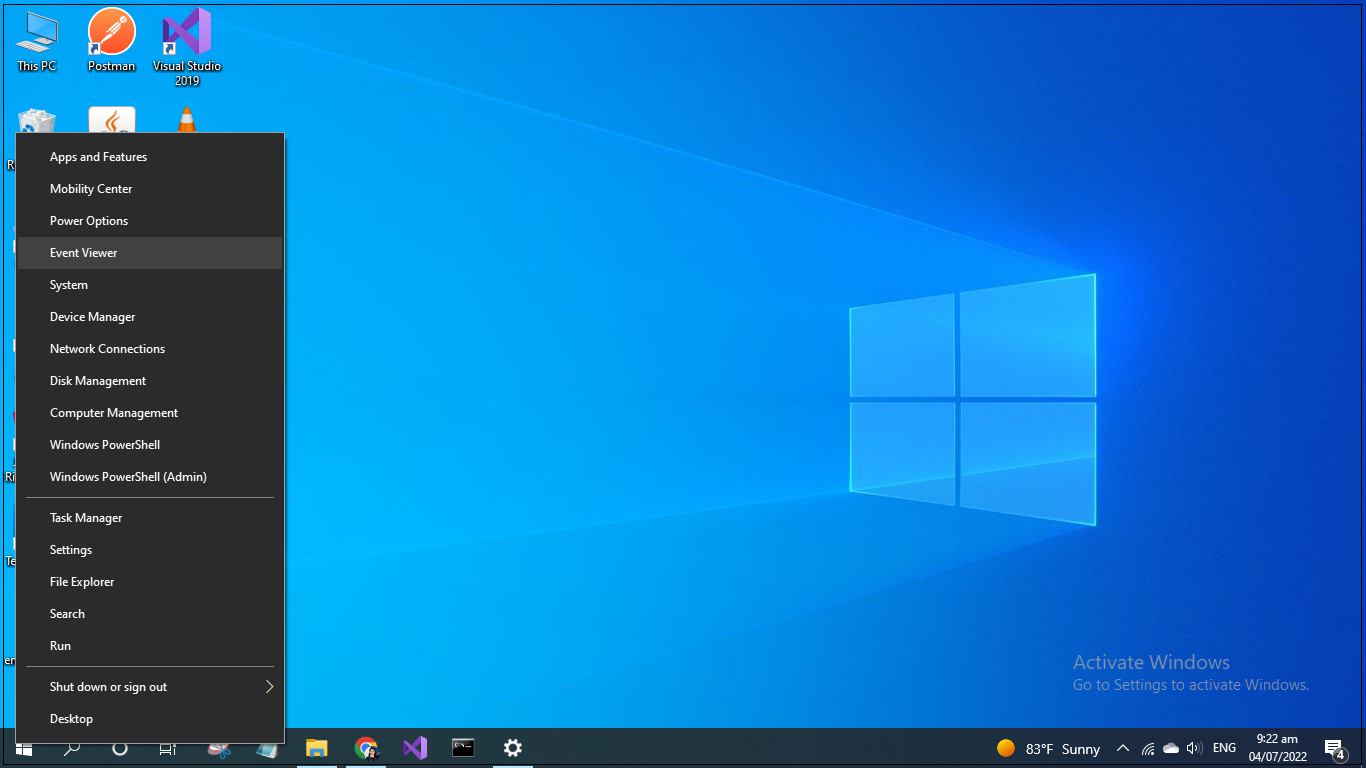
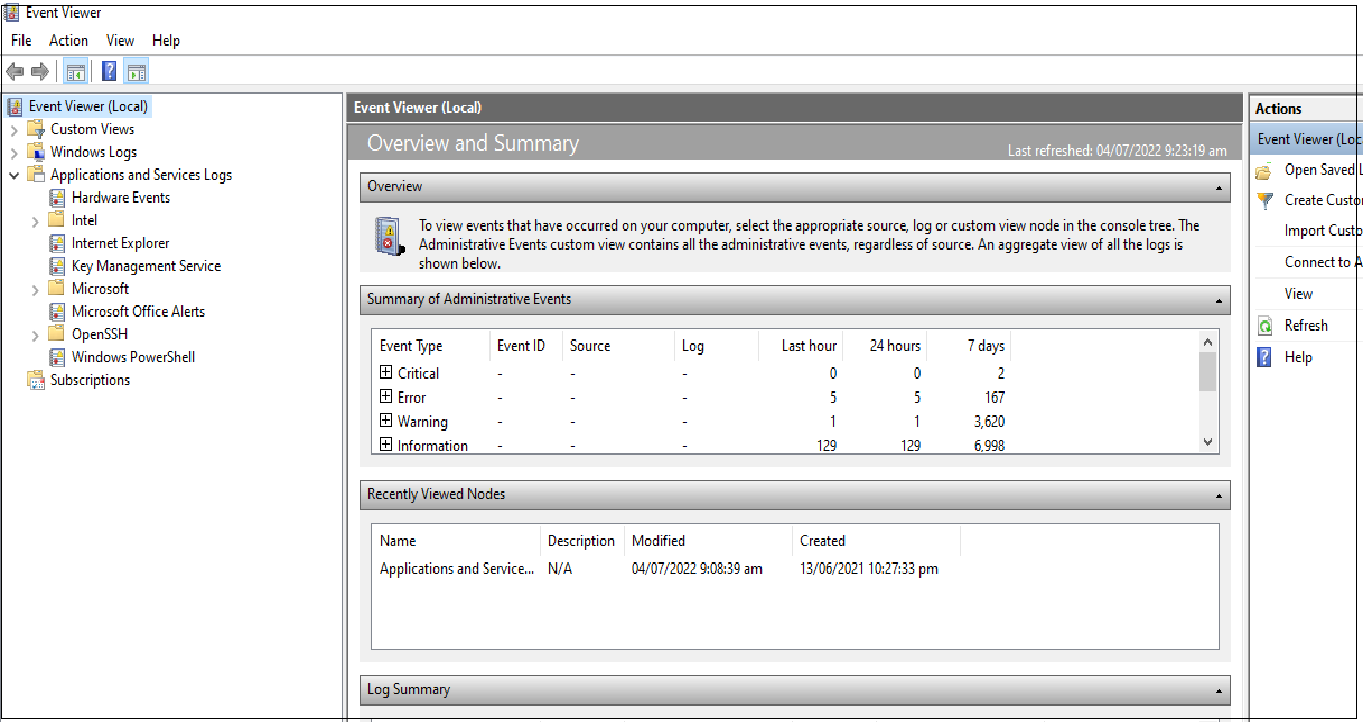
-
Then go to the Applications and Services logs > Microsoft > Windows > DeviceManagement-Enterprise-Diagnostics-Provider > Admin.